Executive Summary
The MS08-067 vulnerability was a remote code execution vulnerability that affected Windows XP and Windows 2003 systems. This vulnerability was first exploited by the Conficker worm, which used the SMB protocol to propagate across networks and infect systems.
The vulnerability was exploited by sending a specially crafted RPC (Remote Procedure Call) request to the vulnerable system, which could then be used to install malware, create new user accounts, or perform other malicious activities.
The Conficker worm used this vulnerability to propagate by exploiting unpatched systems and spreading through the network by accessing the IPC$ share while copying itself to other systems.
Legacy systems that still run unsupported operating systems still exist today in many production environments. Microsoft released a security patch to address the MS08-067 vulnerability in October 2008 but many systems still remain unpatched. ICS systems for example may run on older hardware/software which is not compatible with the latest technology, upgrading these systems may require significant time, effort, and expense. Further complicating matters, many of these systems which are often used in critical infrastructure cannot be taken offline for maintenance or updates without significant disruption to operations.
The intent and output of this threat hunt will be to provide Suricata/Snort detections in an ordered format which may be used to detect if a remote exploit is being executed. In addition, pseudo code will be provided to hunt recursively for such activity within Zeek/Bro metadata logging. The outputs of the detections and hunts will then verify the initial hypothesis generated.
Network Artifacts
The MS08-067 exploit takes advantage of a buffer overflow vulnerability in the Microsoft Server service (srvsvc.dll), which allows an attacker to execute arbitrary code with SYSTEM-level privileges.
To successfully exploit this vulnerability, the attacker must establish a remote connection to the target system and then send a specially crafted packet to the Server service. The packet will contain the exploit code, which is designed to overwrite certain areas of memory with instructions that will ultimately allow the attacker to take control of the system.
The IPC$ share is commonly used to establish remote connections to Windows systems using the Server Message Block (SMB) protocol, which is also used by the Server service. By accessing the IPC$ share, the attacker can connect to the target system and establish a session with the Server service, which allows them to send the exploit code and trigger the vulnerability as shown in Figure 1.
Figure 1 - Wireshark - IPC$
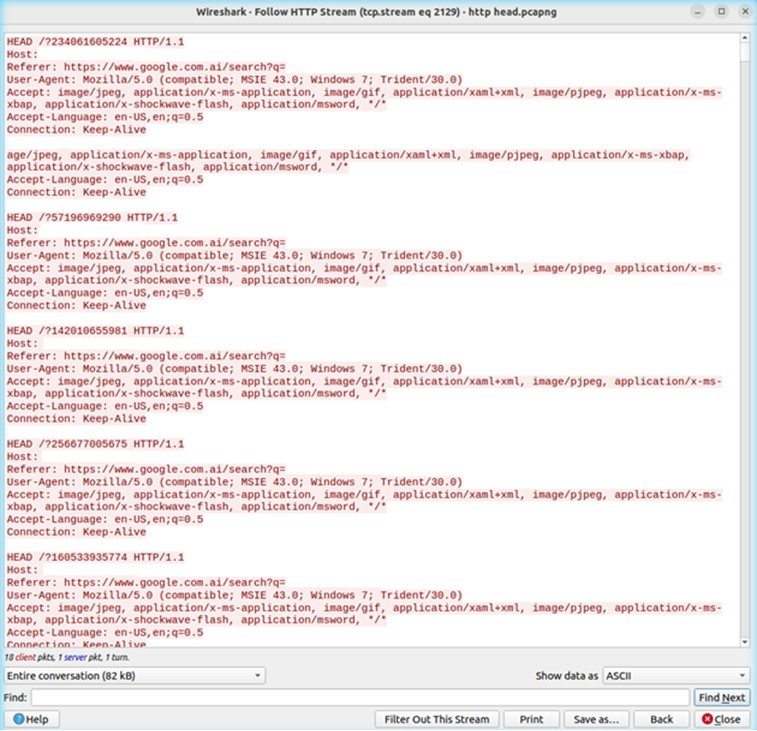
Named pipes are primarily used for local processes to communicate with each other, but can facilitate communication between two processes on separate hosts over SMB. This is a popular technique within Metasploit and a configurable option as well. If IPC$ shares being accessed along with named pipe usage is not common, this can also serve as a starting point to delve deeper onto the endpoint for further investigation. Figure 2 shows what this would look like as network telemetry.
Figure 2 - Wireshark - Pipes
Detection Guidance
To detect the entire attack chain, the following detection guidance will trigger in the following order. Ideally these signatures, should be instrumented within a targeted internal environment where legacy systems reside.
alert tcp $EXTERNAL_NET any -> $HOME_NET 445 (msg:\"GPL NETBIOS SMB-DS IPC$ share access\"; flow:established,to_server; content:\"|00|\"; depth:1; content:\"|FF|SMBu\"; within:5; distance:3; byte_test:1,!&,128,6,relative; byte_jump:2,34,little,relative; content:\"IPC|24 00|\"; distance:2; nocase; flowbits:set,smb.tree.connect.ipc; classtype:protocol-command-decode; sid:2102465; rev:9; metadata:created_at 2010_09_23, updated_at 2010_09_23;)
Detection #1 - IPC$ share access
alert tcp any any -> $HOME_NET 445 (msg:\"ET NETBIOS Microsoft Windows NETAPI Stack Overflow Inbound - MS08-067 (15)\"; flow:established,to_server; content:\"|1F 00|\"; content:\"|C8 4F 32 4B 70 16 D3 01 12 78 5A 47 BF 6E E1 88|\"; content:\"|00 2E 00 2E 00 5C 00 2E 00 2E 00 5C|\"; reference:url,www.microsoft.com/technet/security/Bulletin/MS08-067.mspx; reference:cve,2008-4250; reference:url,www.kb.cert.org/vuls/id/827267; reference:url,doc.emergingthreats.net/bin/view/Main/2008705; classtype:attempted-admin; sid:2008705; rev:5; metadata:created_at 2010_07_30, updated_at 2010_07_30;)
Detection #2 - NETAPI Stack Overflow
Hunting Process
A network traffic analyzer like Zeek can provide visibility into SMB traffic, such as the above packet capture. Since named pipes are treated like files, they show up within the name field. The SMB::FILE_OPEN field in the smb_files.log can be used to drill down further for this activity. The UID field could also be used to correlate the different log files together. Using these logs will be helpful if signatures fired today, and you needed to hunt recursively over an extended period of time.
{"ts":1634092925.899548,"uid":"CXjioG18zBnfPANIJf","id.orig_h":"192.168.1.69","id.orig_p":43183,"id.resp_h":"192.168.1.70","id.resp_p":445,"action":"SMB::FILE_OPEN","name":"\\BROWSER","size":0}
{"ts":1634092925.942094,"uid":"CXjioG18zBnfPANIJf","id.orig_h":"192.168.1.69","id.orig_p":43183,"id.resp_h":"192.168.1.70","id.resp_p":445,"action":"SMB::FILE_OPEN","name":"\\BROWSER","size":0}
{"ts":1634092925.970923,"uid":"CXjioG18zBnfPANIJf","id.orig_h":"192.168.1.69","id.orig_p":43183,"id.resp_h":"192.168.1.70","id.resp_p":445,"action":"SMB::FILE_OPEN","name":"\\SPOOLSS","size":0}
{"ts":1634092925.99429,"uid":"CXjioG18zBnfPANIJf","id.orig_h":"192.168.1.69","id.orig_p":43183,"id.resp_h":"192.168.1.70","id.resp_p":445,"action":"SMB::FILE_OPEN","name":"\\SPOOLSS","size":0}
{"ts":1634092926.024359,"uid":"CXjioG18zBnfPANIJf","id.orig_h":"192.168.1.69","id.orig_p":43183,"id.resp_h":"192.168.1.70","id.resp_p":445,"action":"SMB::FILE_OPEN","name":"\\BROWSER","size":0}
Zeek - smb_files.log
{"ts":1634092920.976657,"uid":"CXjioG18zBnfPANIJf","id.orig_h":"192.168.1.69","id.orig_p":43183,"id.resp_h":"192.168.1.70","id.resp_p":445,"path:\\\\192.168.1.70\IPC$","service":"IPC","share_type":"PIPE"}
References
https://github.com/rapid7/metasploit-framework/blob/master/modules/exploits/windows/smb/ms08_067_netapi.rb
 Figure 4 - Ubuntu VM - Snort - snort.conf
Figure 4 - Ubuntu VM - Snort - snort.conf